Introduction
Every small business uses technology to aid different operations, generate more leads, communicate with clients, and record exponential brand growth. However, this opens up businesses to the risk of being cyberattacked.
A cyberattack is simply an attack against the website of a particular business, leading to consequences that may cripple the business, either temporarily or permanently.
This article will discuss basic and advanced cybersecurity tips necessary for small businesses.
The State of Cybersecurity for Small Businesses
The False Sense of Security
Many small business owners believe they are too small for hackers to target. This is not true. Small businesses should know that it is easy to attack smaller companies because they spend very little on security procedures. This leads to financial, material, and emotional damage to the company. It is, therefore, important that every business, no matter the size, keep its data and information safe to prevent cyberattack consequences.
The Steps Involved in a Cyber Attack
- The hacker’s first step is to hack the company’s website or software and access all available information.
- After getting access, the hacker finds vulnerabilities that they can use to make demands or affect the company.
- Attack: The hacker then deploys malware to shut down the company’s system or steal some data for exploitation and demands.
- Demand: Afterwards, the hacker uses the stolen information to demand money or ransom from the company, steal the personal financial details of the company’s customers, and withdraw money from their bank accounts.
Consequences of a Data Breach to the Company
1. Damage to the company’s reputation
When a cyberattack occurs, it is often glaring to the public. The customers realise that the company has been breached; the news spreads, and the company’s reputation is reduced to dust. The customers lose faith in the company and turn to patronising other competitors. The company strives to salvage the situation, but this takes a while, and there is a possibility that the company will not recover.
2. Financial Losses
Financial losses as a result of a security breach can affect the company in various ways. The company would need to spend a large amount of money on compensation to the affected customers, repay any money lost as a result of the breach, pay the hacker a ransom, pay some money to the cybersecurity expert who would help contain the malware, and so on.
3. Legal Issues
Some companies store customers’ personal or financial information on their websites. Such websites, e.g., casino sites, banking, and finance businesses, have customers’ financial information on the web. Whenever there is a security breach, the information is exposed, and the hacker may access it and use the data to steal funds from the customer’s account. This procedure often leads to legal suits against the company by the customers for the leak of their personal information.
4. Operational Downtime
It is imperative for any business experiencing a security breach to have downtime in its operations; this is because, before the cyberattack can be contained, certain steps must be taken, e.g., identifying the source of the malware, highlighting steps to effectively cub the cyberattack, and gradually implementing those steps. This step-by-step procedure may take a couple of days or weeks before the attack is eventually mitigated.
5. Loss of Competitive Edge
It is quite common for competitors to take advantage of each other, and this also occurs in the case of cyber attacks. Competitors will target long-term customers of the business and draw them to themselves instead. The competitors will take the downfall of the company as an advantage to take under their wing all of the company’s partners and customers, resulting in temporary or permanent loss of customers for the attacked business.
6. Emotional Stress
Getting attacked and finding the proper solution to security attacks can cause a lot of emotional and mental stress, draining both the company’s management and its employees.
Basic Cybersecurity Tips for Small Businesses
1. Firewalls and Network Security
Firewalls are barriers that help restrict unauthorised access and prevent hacking attacks. They monitor outgoing and incoming traffic and automatically block suspicious activity on the website by logging the person out. Network security serves as a detection barrier to filter out threats and block unauthorised access to the business network. Firewalls and network security are quite effective in cybersecurity and they should always be kept active.
2. Encryption and Backup Strategies
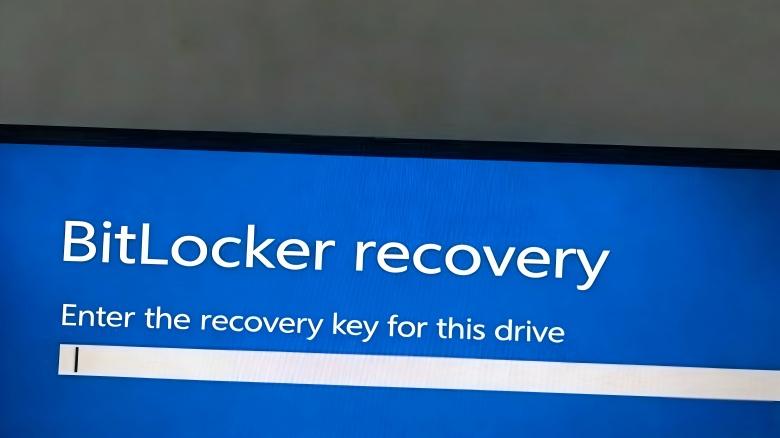
Encryption is one of the most effective ways to protect your business data. It scrambles information so only authorised users can access it, making it unreadable to hackers. Apply encryption to emails, files, and sensitive business data stored on your devices or shared online. This extra layer of security ensures critical information remains private, even if intercepted.
Backing up your data is equally important. Regularly save copies of your files on-site (like external hard drives) and in the cloud. This dual backup strategy ensures you can recover essential data quickly in case of a cyber attack, system failure, or accidental deletion.
Advanced Cybersecurity Measures for Small Businesses
1. Threat Intelligence and Monitoring
Threat intelligence means staying informed and regularly checking and auditing the company’s systems to detect any security breaches on time and reduce the consequences. Monitoring tools scan the systems regularly for any sign of potential breach or suspicious behaviour of a user on the website. These tools are programmed to sound an alarm in case of a possible threat, enabling the company or security team to respond quickly.
2. Penetration Testing and Vulnerability Assessments
Penetration testing, often called “pen testing”, is a trial cyber attack launched by ethical hackers to test the strength of the company’s systems. These tests help uncover system vulnerabilities, such as weak passwords or misconfigured systems. These findings are used to determine potential entry points of hackers, and prompt action is taken to strengthen these vulnerabilities. At the same time, vulnerability assessment identifies and prioritises all security gaps. These assessments are done by scanning the company’s systems, applications, and networks for vulnerabilities and allocating resources to fix the vulnerabilities.
3. Incident Response and Disaster Recovery Planning
An incident response plan (IRP) is a plan with steps implemented in case of a cyberattack. The plan always involves steps to identify the breach, contain the damage, eradicate the threat, determine who to contact, and recover.
As the name implies, a disaster recovery plan (DRP) is a set of steps to recover from a cyberattack. These steps usually include data backup both on-site and in the cloud, alternative communication channels, and so on. IRP and DRP work together to ensure that the company suffers minimal loss during and after a cyberattack.
Final Words
Cybersecurity concerns both small and big businesses. However, small businesses need to take cybersecurity seriously. Various simple and advanced cybersecurity measures can reduce the risk of being hacked or attacked. As stated in the article above, these principles are quite easy to understand and implement.
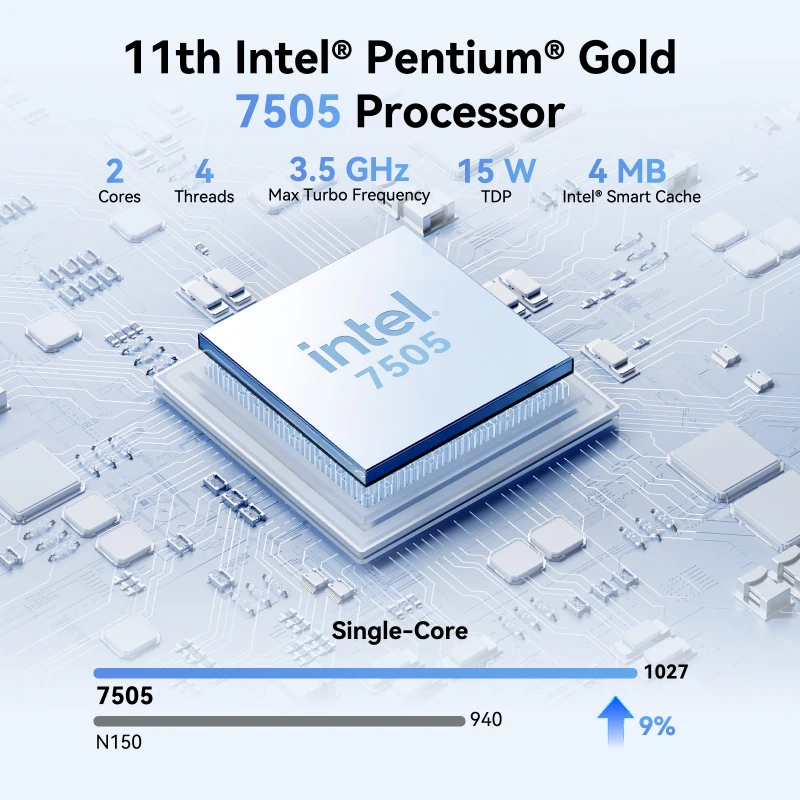
Additionally, using the right tools is important in preventing cyber attacks. For example, some devices work well with any form of cybersecurity measure. For example, the GEEKOM Air12 Mini PC Intel® Pentium® Gold 7505 is pre-installed with the genuine operating system Windows 11 Pro; it’s a versatile computer that is compact in size and good for security.
Therefore, investing in computers with genuine operating systems can make sure the cybersecurity measures discussed are easy to implement and also make hacking or cyber-attacks almost impossible. For more options, explore mini PCs for small businesses or check out the best computers for small businesses.
FAQs
Why is cybersecurity critical to small businesses?
Cybersecurity is important to all businesses. Cybercriminals often target small businesses because of their weak defences, but cybersecurity helps to protect, shield, and defend them from cyberattacks.
What is the most basic way of improving cybersecurity?
The most basic form of cybersecurity is to use a pre-installed OS computer instead of a cracked version of the operating system. Then, a strong password should consist of upper- and lowercase letters, numbers, and special characters.
How often should a backup be done?
If convenient, you should back up your files, data, and information every day, both on your phone or mobile device and in the cloud.